Azure Sentinel is a
SIEM (security information event management) and
SOAR (security orchestration automated response) system in Azure. This means that incidents and security threats can be detected and alerted. You can use it to investigate and mitigate threats. You can gain insight into collected data, events and potential harmful incidents through overviews, dashboards and custom queries. Once an accident occurs, you can choose to launch the Azure Sentinel Playbook, a logical application that begins the automatic mitigation process.
Azure Sentinel four crucial areas or stages:
- Collect. Collecting data from multiple sources and clouds, on-premises, applications, infrastructure, users, services, and others.
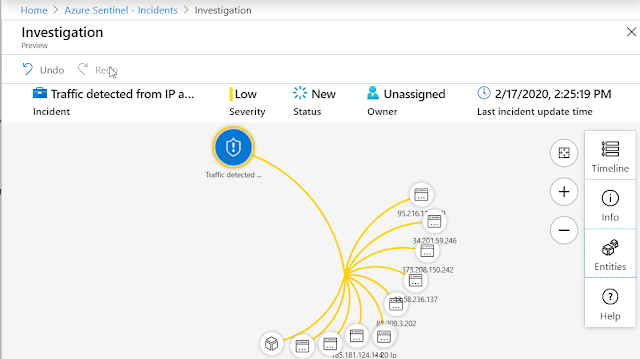
- Detect. Detect threats to protected and monitored resources as they happen, minimizing the time to react to threats.
- Investigate. Powered with artificial intelligence, search for and discover malicious activities across all protected assets.
- Respond. Once a threat is known, avoid manual actions and respond to threats with automating tasks.
What does it cost?
- Capacity Reservation based pricing
- Capacity Reservation is a fixed-fee license, where you pay for capacity (and receive discounts based on the amount of capacity you purchase).
- Purchasing capacity for 100 GB per day will cost you 109.63 € ($123)/day
- Pay-As-You-Go
- The first 5 GB is free, then per GB you’d pay 2.522 € ($2.99).
- Pay-As-You-Go is based on Log Analytics pricing, and it’s set at 2.20 € ($2.60)/GB.
What about Azure Security Center?
- ASC is more about getting and understanding how to best configure your Azure assets
- Azure Sentinel is all about detecting bad actors from accessing your data.
Data Retention
Once Azure Sentinel is enabled on your Azure Monitor Log Analytics workspace, every GB of data ingested into the workspace can be retained at no charge for the first 90 days. Retention beyond 90 days will be charged per the standard
Azure Monitor Log Analytics retention prices.
Advanced multistage attack detection in Azure Sentinel
- Anomalous login leading to O365 mailbox exfiltration
- Anomalous login leading to suspicious cloud app administrative activity
- Anomalous login leading to mass file deletion
- Anomalous login leading to mass file download
- Anomalous login leading to O365 impersonation
- Anomalous login leading to mass file sharing
- Anomalous login leading to ransomware in cloud app
On-board Azure Sentinel
To on-board Azure Sentinel, you first need to enable Azure Sentinel, and then connect your data sources. Azure Sentinel comes with a number of connectors for Microsoft solutions, you’ll need to create a new Log Analytics-based workspace. If you have any existing ones, you can choose to use one of those, or just create a new empty one.
Global prerequisites
- Active Azure Subscription
- Log Analytics workspace.
- Contributor permissions
Connect data sources
- Machines and virtual machines: you can install the Azure Sentinel agent that collects the logs and forwards them to Azure Sentinel.
- Firewalls and proxies: Azure Sentinel utilizes a Linux Syslog server. The agent is installed on it and from which the agent collects the log files and forwards them to Azure Sentinel.
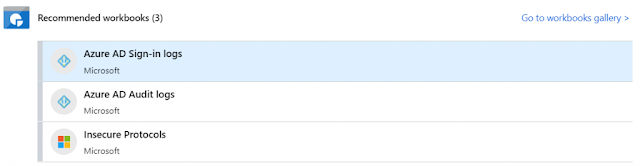
Once a connector has been configured, you can click on
Next steps to see additional guidance on how to best utilize the connector. For Azure Active Directory, the options include additional workbooks, and a few query samples using Log Analytics’ query language, KQL (also sometimes known as Kusto).
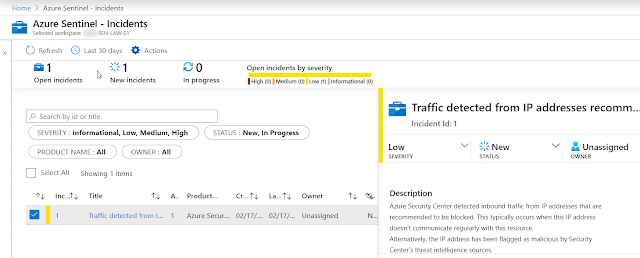
Azure Sentinel: Incidents
Azure Sentinel can collect data from all sorts of data sources, like the Azure Security Center, Azure Active Directory, Office 365, Amazon Web Services, CyberArk and more. It can detect incidents in the data from those data sources and alert you that something needs your attention. Once an accident occurs, you can choose to launch the Azure Sentinel Playbook, a logical application that begins the automatic mitigation process.
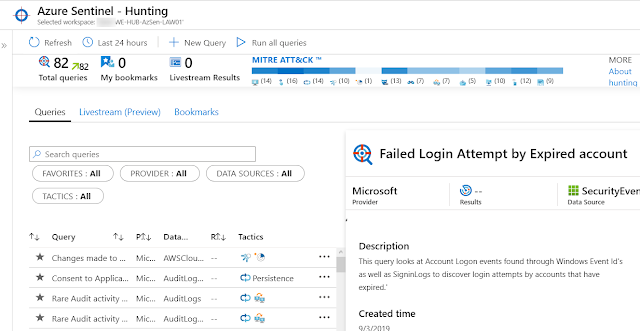
Azure Sentinel: Hunting
Hunting in this context means that investigators run queries, investigate and use playbooks (known as notebooks in Azure Sentinel lingo) to proactively look for security threats.
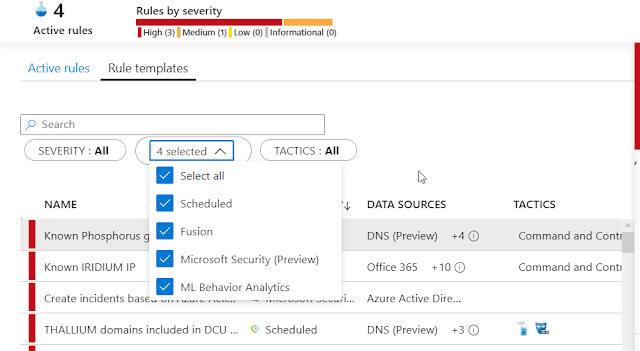
Azure Sentinel: Detecting threats
After you
connected your data sources to Azure Sentinel, you want to be notified when something suspicious happens. To enable you to do this, Azure Sentinel provides you with out-of-the-box built-in templates.
- Use out-of-the-box detections
- Automate threat responses
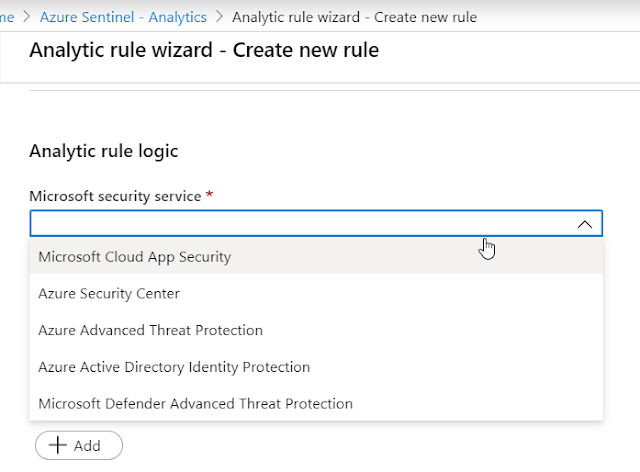
You can choose between Azure Security Center, Cloud App Security, Azure ATP, and Azure AD Identity Protection.
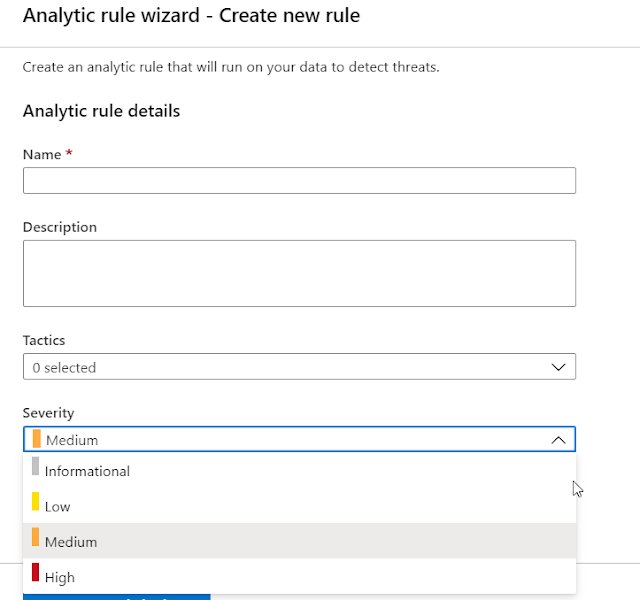
If you want more freedom, use
Scheduled query rule when creating the rule. This will allow you to select which tactics to watch for, and what severity level we’re interested in.
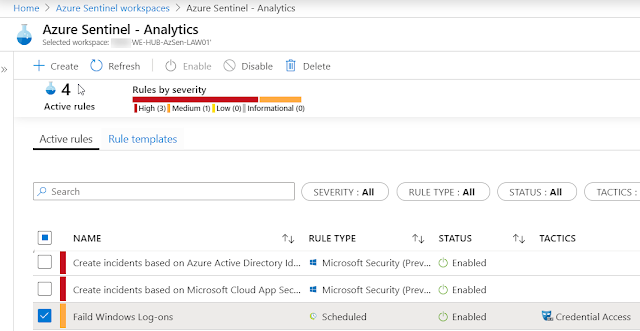
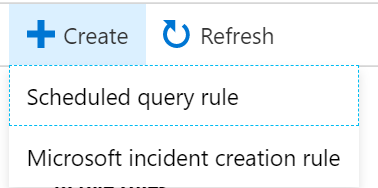
To build your detection rules, click
Azure Sentinel > Analytics. Click
+ Create to add a new rule.
With the use of
Scheduled query ruleyou have to create a custom query, and set your scheduling as well as alerts threshold.
Also, you can execute a playbook based on the triggered alert.
Azure Sentinel – Analytic rule
You can create a rule based on a scheduled query (using the query language in Log Analytics), or use a pre-defined service-triggered rule – such as an alert from Azure Security Center. I’ll choose the latter –
Microsoft incident creation rule –as it’s a bit more explanatory to what happens when detecting a threat.
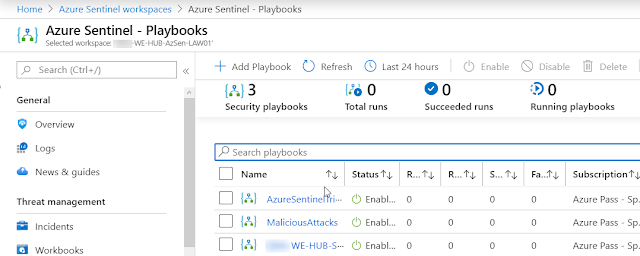
Azure Sentinel: Playbooks
After creating your detection rules and alerts, now it’s time to start creating your playbooks constructing logic app workflows. Also, you would be able to create an automated response to those detected threads.
Azure Sentinel – Workbooks Templates:
- AWS Network Activities
- AWS User Activities
- Azure Activity
- Azure AD Audit logs
- Azure AD Sign-in logs
- Azure Firewall
- Azure Information Protection
- Azure Network Watcher
- Check Point Software Technologies
- Cisco
- CyberArk Privileged Access Security
- DNS
- Exchange Online
- F5 BIG-IP ASM F5
- FortiGate
- Identity & Access
- Insecure Protocols
- Juniper
- Linux machines
- Microsoft Web Application Firewall (WAF)
- Office 365
- Palo Alto Networks
- Palo Alto Networks Threat
- SharePoint & OneDrive
- Symantec File Threats
- Symantec Security
- Symantec Threats
- Symantec URL Threats
- Threat Intelligence
- VM insights